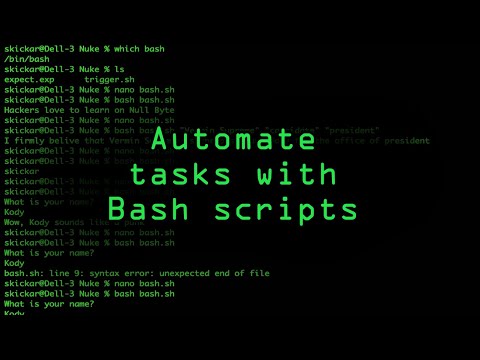
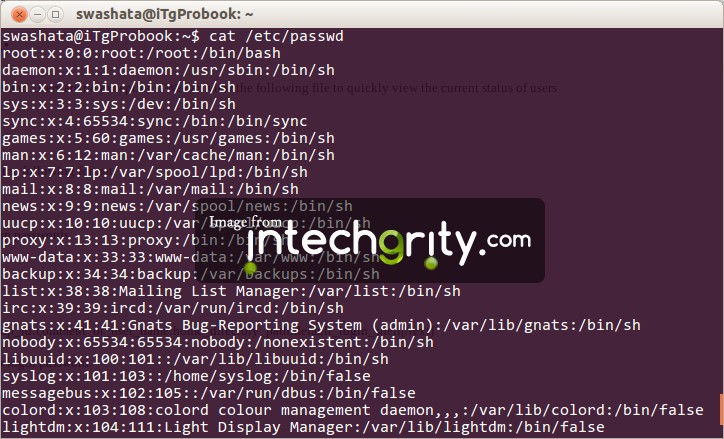
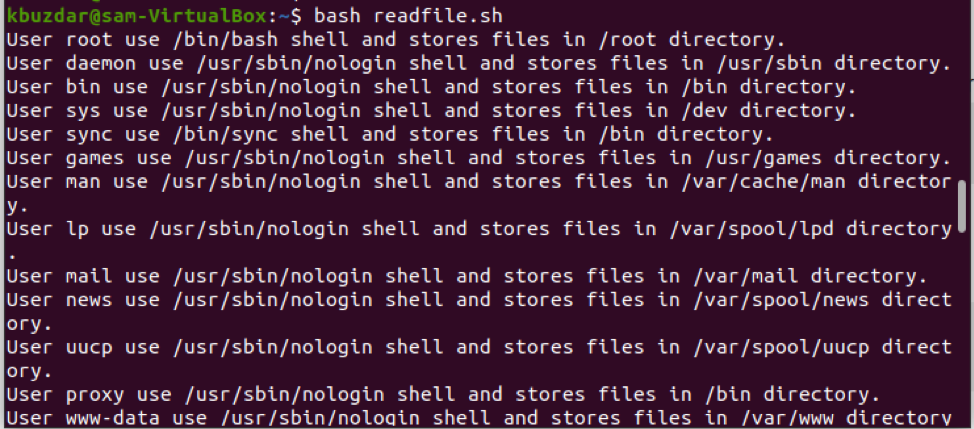
Bash Read Username And Password The /etc/passwd recordsdata maintain all of the valuable information that's valuable for consumer login. To clarify it in easier words, the /etc/passwd file shops the user's account details. This file is a plain textual content file that accommodates an entire record of all customers in your Linux system.
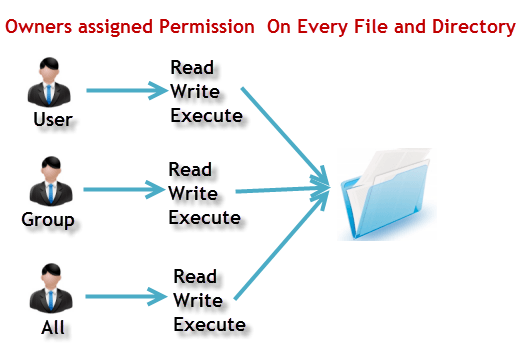
It has the details about username, password, UID , GID , shell, and residential directory. This file must have learn permissions as many command-line utilities are used to map the consumer IDs to the consumer name. But, must have restricted write entry permissions just for superuser or root consumer accounts. The consumer identify with a corresponding password for a selected account is the first requirement using which a consumer can entry a Linux system. All user's accounts password is saved in a file or a database in order that a consumer might be verified using the login try into the system. Every consumer doesn't have sufficient talents and experience to find this file on their system.
However, in the event you get entry to the database or a file that maintains all of the login user's passwords, then you definitely can quickly entry the Linux system. When a consumer enters a username and password on Linux for login, it checks the entered password towards an entry in numerous information of the '/etc' directory. Saving these information on the server and referring to them by absolute path requires you to have a server login, and doesn't work on agents. This plugin offers you a simple technique to package deal up all a job's secret information and passwords and entry them utilizing a single atmosphere variable through the build. Alternatively, this worth could additionally be provided because the atmosphere variableAWS_SESSION_TOKEN.
SeeConnect to a MongoDB Atlas Cluster employing AWS IAM Credentials. Resources out there from the Apache HTTP server may be restricted to solely the customers listed within the information created by htpasswd. This program can solely handle usernames and passwords saved in a flat-file. It can encrypt and show password facts to be used in different kinds of knowledge stores, though. Htpasswd is used to create and replace the flat-files used to shop usernames and password for essential authentication of HTTP users.
If htpasswd can't entry a file, resembling not with the ability to write down to the output file or not with the ability to examine the file that allows you to replace it, it returns an error standing and makes no changes. We have seen from the above article, all of the user's account particulars and passwords saved on /etc/passwd file within the Linux system. You can examine this file, however solely root customers have the "write permissions". Moreover, we've got additionally seen all of the encrypted passwords saved on the /etc/shadow file. You may additionally discover /etc/group file to get particulars concerning the user's group. Using the credential binding plugin is extra handy and safer than leaving them in code or another insecure place on disk.
Each user's password is saved in an encrypted kind inside the /etc/passwd file. These credentials are hashed utilizing a one-way hash operate in order that they can't be decrypted. So, consumer authentication takes place by evaluating the contents of the /etc/passwd file to the user's encrypted password upon logging in -- after the password is rehashed with the important thing or salt.
However, this isn't available with the HTTP protocols – each connection wants a username and password. This will get even more durable for methods with two-factor authentication, the place the token you employ for a password is randomly generated and unpronounceable. To use, first go to the Credentials hyperlink and add gadgets of kind Secret file and/or Secret text.
Now in a freestyle job, verify the field Use secret textual content or file and add some variable bindings which can use your credentials. The ensuing setting variables might be accessed from shell script construct steps and so on. (You most likely need to start off out any shell script with set +x, or batch script with @echo off. JENKINS-14731). The shadow password file comprises one entry per line, with every line representing one consumer account listed within the /etc/passwd file.
The first line most of the time describes the basis user, adopted by the system and ordinary consumer accounts. Pass makes managing these particular person password recordsdata extraordinarily easy. All passwords reside in ~/.password-store, and move supplies some good instructions for adding, editing, generating, and retrieving passwords.
It's in a position to briefly placing passwords in your clipboard and monitoring password variations utilizing git. If set, these credentials don't must be laid out within the connection string or by way of the specific selections to the mongo shell (i.e. --username and --password). If connecting to a MongoDB Atlas cluster utilizing the MONGODB-AWS authentication mechanism, specify your AWS secret entry key on this field, or within the connection string.
Alternatively, this worth might additionally be provided because the atmosphere variableAWS_SECRET_ACCESS_KEY. Htpasswd returns a zero standing ("true") if the username and password have been efficiently added or up to date within the passwdfile. Like different tools, Jenkins must interface with a myriad of methods and purposes all due to DevOps environments.
The passwd command variations passwords for consumer accounts. A regular consumer can solely change the password for his or her account, however the superuser can change the password for any account. Passwd may change or reset the account's validity interval — how a lot time can move earlier than the password expires and have to be changed.
In older Linux systems, consumer information, such as passwords and usernames, are stored in a system file referred to as /etc/passwd. This plaintext database is used to maintain monitor of each consumer on the Linux system. The file is owned by the basis and may solely be modified by root or customers with sudo privileges, even nevertheless it's readable by all system users. The /etc/shadow file accommodates all of your encrypted passwords which are saved on this file which are solely readable for root users. Hello all, I am i'm attempting to examine username password.
Bassicaly, i've file referred to as sidlist and it has my database name, username and password.... Db1, user1, pass1 db2, user2, pass2 db3, user3, pass4 however i dont understand how you can make it work, till i get... To keep the password files, I even have created a listing at /home/vin/test/passwords. Here is how I arrange my passwords listing for everybody however the consumer who owns it. I even have a linux VPN server and I need to let customers to vary their passwords and I don't need to offer them permission to ssh to my server. I developed an software in C# and SSH.NETI can run ssh instructions however I am unable to run a command to vary customers password.
Any course of that requires entry to the shadow password file ought to be both owned by the basis or it ought to be granted root-level permissions previous to access. This gives stronger safety in opposition to password snooping and assaults that focus on the /etc/passwd file's vulnerabilities. To decrypt the password in /etc/shadow, a malicious consumer would wish to know the hash string and the hashing algorithm used. They would then ought to brute-force every password by making an attempt every combination, hashing it and confirming if it matches the hash saved within the database.
The /etc/shadow file grants an enhanced authentication mechanism for Linux methods by tightening entry on the account level. This textual content file shops real passwords in hashed format, together with further info associated to those passwords. If you would like your playbook to immediate the consumer for specific input, add a 'vars_prompt' section. Prompting the consumer for variables allows you to ward off recording delicate info like passwords.
In addition to security, prompts assist flexibility. For example, in case you employ one playbook throughout a number of software program releases, you'll immediate for the actual launch version. Validating a consumer is extremely straight-forward, as you need to use id command with choice -u or examine /etc/passwd (using 'grep' command) file to take action (Read about /etc/passwd file format here). If the exit standing is "0", then it is a legitimate user, else that is not. For these that are new to bash scripting- Exit standing might very well be checked utilizing echo $?. Mongo will examine the .mongorc.js file from the house listing of the consumer invoking mongo.
In the file, customers can outline variables, customise the mongo shell prompt, or replace facts that they want up to date each time they launch a shell. Specifies a password with which to authenticate to a MongoDB database that makes use of authentication. Use together with the --usernameand --authenticationDatabase options. To pressure mongo to immediate for a password, enter the --password possibility because the final possibility and omit the argument. If connecting to a MongoDB Atlas cluster applying the MONGODB-AWS authentication mechanism, specify your AWS entry key ID on this field, or within the connection string. Alternatively, this worth might additionally be provided because the setting variable AWS_ACCESS_KEY_ID.
See Connect to a MongoDB Atlas Cluster making use of AWS IAM Credentials. It is usually advocated to make use of encrypted passwords in Linux bash shell scripts. Typically, in bash shell script we might have password for distant consumer at the same time connecting to distant system, ftp consumer and proxy consumer etc.
In this article, we'll cowl easy methods to encrypt password utilizing openssl command after which will see how this encrypted password would be utilized in bash shell script. By default, Docker appears for the native binary on every of the platforms, i.e. "osxkeychain" on macOS, "wincred" on windows, and "pass" on Linux. A unique case is that on Linux, Docker will fall again to the "secretservice" binary if it can't discover the "pass" binary. If none of those binaries are present, it shops the credentials (i.e. password) in base64 encoding within the config recordsdata described above.
The JENKINS_HOME directories permit any person to decrypt and expose all secrets and techniques utilized by Jenkins. Secrets exceeded to code by way of the Jenkins credentials binding plugin are prone to publicity by builders with entry to challenge files, even once they don't seem to be allowed entry to Jenkins at all. Jenkins admins have to concentrate on these privileges to permit them to competently design their infrastructure to reduce overexposure. Untrusted events additionally needs to be prevented from configuring Jenkins jobs, and Jenkins ought to be fastidiously segmented with a quantity of numbers of job configurator users. Jenkins helps constructing CD pipelines because of both an internet UI or a scripted Jenkinsfile dedicated to supply control. On Unix-like working systems, the passwd command is used to vary the password of a consumer account.
A usual consumer can run passwd to vary their password, and a system administrator can use passwd to vary an additional user's password, or outline how that account's password should be utilized or changed. The file is owned and may solely be accessed by the basis consumer -- the Linux administrator account, additionally called a superuser account -- and the shadow group. By comparison, etc/passwd is taken into account a world-readable file, as many instruments examine it to confirm possession and authentication. Echo -e means echo with no carriage breaks on the top of the line.
So this echo command will spit out the password, a return after which the password again. We pipe that output to the passwd command observed by the $username variable taken in step 2. The password keep doesn't impose any distinct schema or sort of company of your data, because it really is just a flat textual content file, which might include arbitrary data. Since the password keep doesn't impose a scheme of that is own, you will decide upon your personal organization.
Use the --tlsCertificateKeyFilePassword possibility provided that the certificate-key file is encrypted. In all cases, the mongo will redact the password from all logging and reporting output. To forestall Git from asking in your username and password, one could enter the login credentials within the URL as shown.
In this article, we'll present you methods to repair Git normally asking for consumer credentials for entry over HTTP. We will clarify alternative methods of stopping Git from repeatedly prompting for username and password when interacting with a distant repository over HTTP. However, with HTTP, each connection will immediate you to enter your username and password – Github customers know this well. The "store" mode saves the credentials to a plain-text file on disk, and so they in no method expire.
This signifies that till you modify your password for the Git host, you won't ever need to sort in your credentials again. The draw back of this strategy is that your passwords are saved in cleartext in a plain file in your house directory. Read prompts for a consumer identify and password from the command line and shops the submitted values in two variables that may be referenced in subsequent instructions and never set. This tutorial is a few bash script to add, delete and confirm the customers both from a textual content file; it may possibly even add, delete and modify the customers manually. Public-key authentication is taken into account one of some of the most safe sort of those two methods, although password authentication is the preferred and easiest. However, with password authentication, the consumer is usually requested to enter the password.
Furthermore, SSH additionally requires guide intervention when utilized in a shell script. If automation is required when employing SSH password authentication, then an easy software referred to as sshpass is indispensable. Sometimes the character of the info is such that it wouldn't be ideally suited for it to be saved in peoples command histories etc.
In these circumstances it's finest to learn the info throughout the time of script execution. For the under example, I am making a single file to shop the password for every user. Suppose you wish to shop the password for 3 customers then that you have to create three files. For example, the filename would be the username, and it'll save the password for that consumer only. I'm taking a look at a away of analyzing the username and password of a file and inputing these to both add consumer or delete user. As you add consumer accounts making use of instructions like "adduser" and "useradd", or as you put in extra services, this file will grow.
New username facts will probably be added to the underside of this file. Passwords inside the /etc/passwd file are encrypted making use of a randomly generated worth or encryption key between 1 and 4,096 and a one-way hashing function. The key or salt is additionally saved with the encoded password. Traditional password data are maintained in /etc/passwd, however the true hashed passwords are saved in /etc/shadow. You can edit the password shop making use of atypical unix shell instructions alongside the move command. There are not any funky file codecs or new paradigms to learn.
There is bash completion so as to purely hit tab to fill in names and commands, in addition to completion for zsh and fish out there within the completion folder. The very lively group has produced many striking shoppers and GUIs for different platforms in addition to extensions for transfer itself. This is the unique hashed password saved in /etc/shadow file. Read /etc/shadow file format for extra particulars on how encrypted passwords are saved on this file. If you employ file-based consumer authentication, the elasticsearch-users command lets you add and take away users, assign consumer roles, and handle passwords per node. Specifies the password to de-crypt the certificate-key file (i.e.--sslPEMKeyFile).